2026-03-25 エディンバラ大学

Image credit: Getty Images / SmileStudioAP
<関連情報>
- https://www.ed.ac.uk/news/deepfake-detection-methods-vulnerable-to-attack
- https://arxiv.org/abs/2512.11771
指紋のにじみ:AI画像指紋の堅牢性に関する体系的な評価 Smudged Fingerprints: A Systematic Evaluation of the Robustness of AI Image Fingerprints
Kai Yao, Marc Juarez
arXiv last revised 21 Jan 2026 (this version, v2)
DOI:https://doi.org/10.48550/arXiv.2512.11771
Abstract
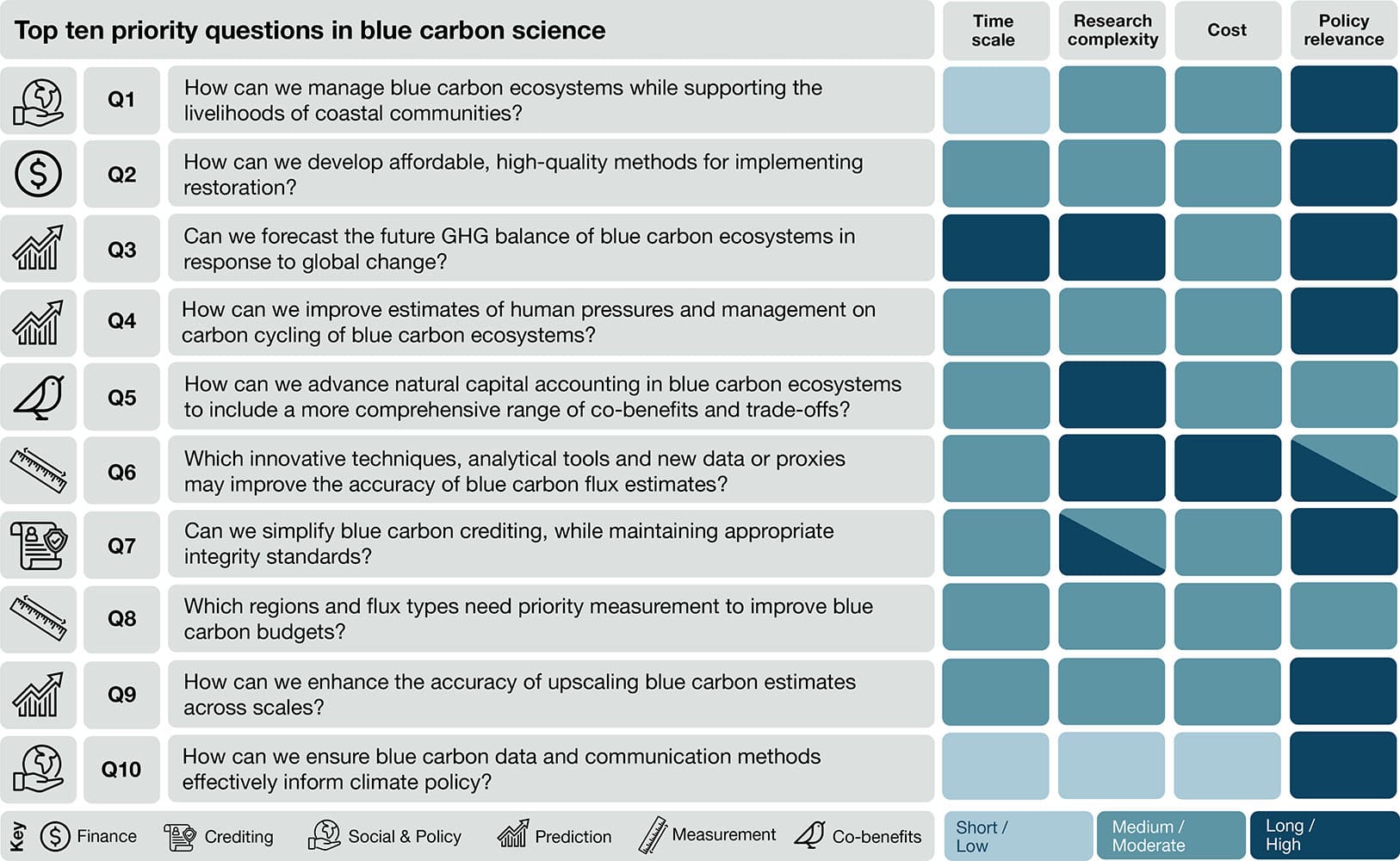
Model fingerprint detection has shown promise to trace the provenance of AI-generated images in forensic applications. However, despite the inherent adversarial nature of these applications, existing evaluations rarely consider adversarial settings. We present the first systematic security evaluation of these techniques, formalizing threat models that encompass both white- and black-box access and two attack goals: fingerprint removal, which erases identifying traces to evade attribution, and fingerprint forgery, which seeks to cause misattribution to a target model. We implement five attack strategies and evaluate 14 representative fingerprinting methods across RGB, frequency, and learned-feature domains on 12 state-of-the-art image generators. Our experiments reveal a pronounced gap between clean and adversarial performance. Removal attacks are highly effective, often achieving success rates above 80% in white-box settings and over 50% under black-box access. While forgery is more challenging than removal, its success varies significantly across targeted models. We also observe a utility-robustness trade-off: accurate attribution methods are often vulnerable to attacks and, although some techniques are robust in specific settings, none achieves robustness and accuracy across all evaluated threat models. These findings highlight the need for techniques that balance robustness and accuracy, and we identify the most promising approaches toward this goal. Code available at: this https URL.