2025-02-25 カリフォルニア大学アーバイン校(UCI)

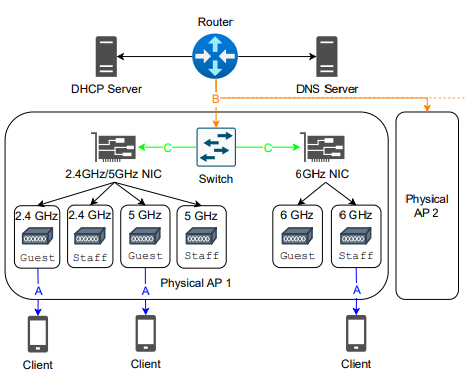
UC Irvine computer scientists used the field at the campus’s Anteater Recreation Center to demonstrate their FlyTrap attack on autonomous drones. Ordinary umbrellas with AI-generated designs can trick the aircraft into moving steadily closer to the umbrella holder, who can then capture them with nets or cause them to crash. The FlyTrap attack methodology spotlights a vulnerability in drone technology utilized in a variety of law enforcement, military and security applications. Shaoyuan Xie / UC Irvine
<関連情報>
- https://news.uci.edu/2026/02/25/uc-irvine-researchers-expose-critical-security-vulnerability-in-autonomous-drones/
- https://arxiv.org/abs/2509.20362
FlyTrap: Physical Distance-Pulling Attack Towards Camera-based Autonomous Target Tracking Systems
Shaoyuan Xie, Mohamad Habib Fakih, Junchi Lu, Fayzah Alshammari, Ningfei Wang, Takami Sato, Halima Bouzidi, Mohammad Abdullah Al Faruque, Qi Alfred Chen
arXiv last revised 28 Jan 2026 (this version, v2)
DOI:https://doi.org/10.48550/arXiv.2509.20362
Abstract
Autonomous Target Tracking (ATT) systems, especially ATT drones, are widely used in applications such as surveillance, border control, and law enforcement, while also being misused in stalking and destructive actions. Thus, the security of ATT is highly critical for real-world applications. Under the scope, we present a new type of attack: distance-pulling attacks (DPA) and a systematic study of it, which exploits vulnerabilities in ATT systems to dangerously reduce tracking distances, leading to drone capturing, increased susceptibility to sensor attacks, or even physical collisions. To achieve these goals, we present FlyTrap, a novel physical-world attack framework that employs an adversarial umbrella as a deployable and domain-specific attack vector. FlyTrap is specifically designed to meet key desired objectives in attacking ATT drones: physical deployability, closed-loop effectiveness, and spatial-temporal consistency. Through novel progressive distance-pulling strategy and controllable spatial-temporal consistency designs, FlyTrap manipulates ATT drones in real-world setups to achieve significant system-level impacts. Our evaluations include new datasets, metrics, and closed-loop experiments on real-world white-box and even commercial ATT drones, including DJI and HoverAir. Results demonstrate FlyTrap’s ability to reduce tracking distances within the range to be captured, sensor attacked, or even directly crashed, highlighting urgent security risks and practical implications for the safe deployment of ATT systems.